Powered by Open Source
We build on the shoulders of giants.





The Great Cloud Repatriation: AWS vs. The Open Source Stack
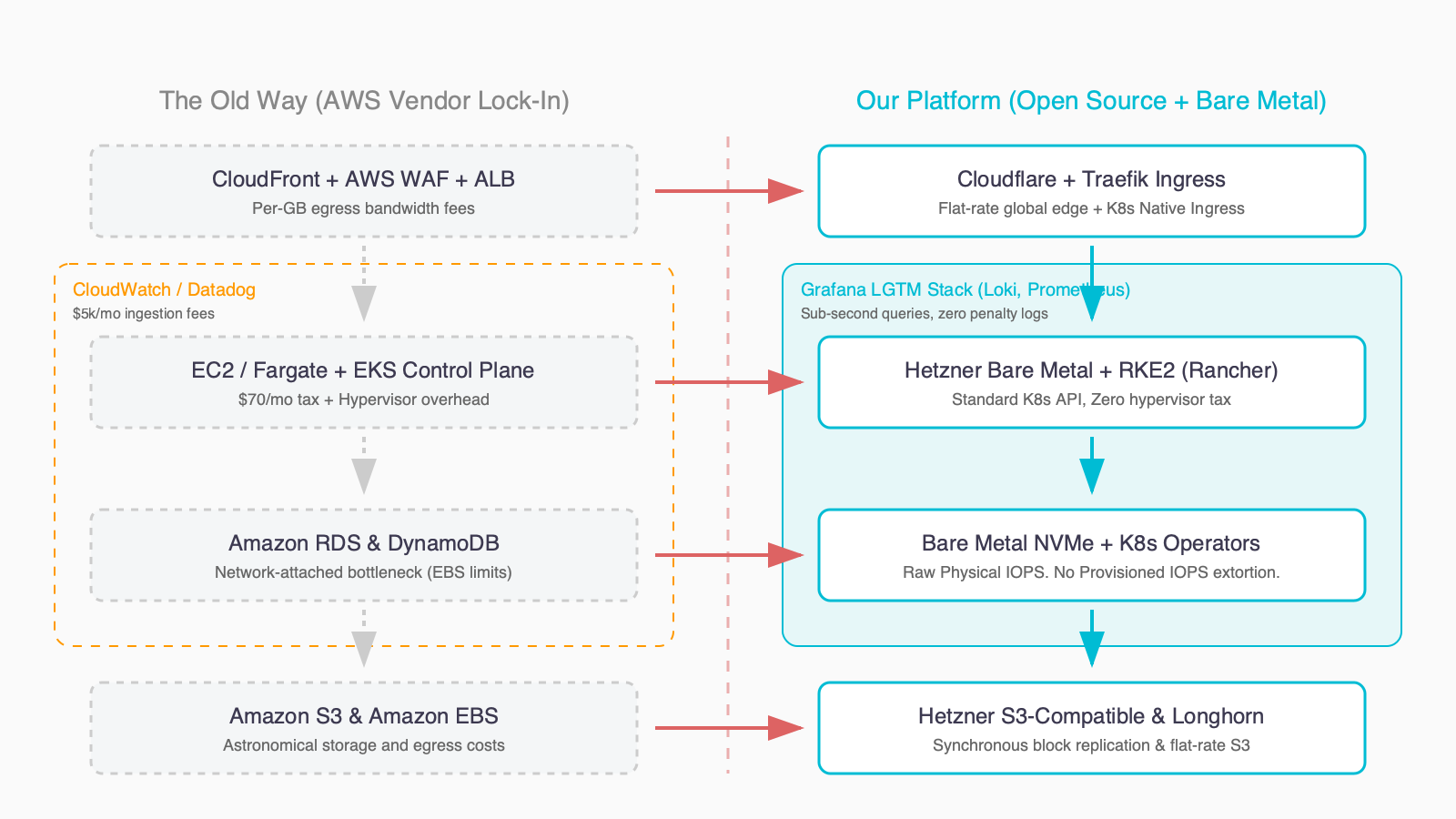
The Stack Matrix: Big Cloud vs. Our Platform
| Feature Category | Big Cloud (AWS / GCP) | Our Open Stack | Why It Matters (The Tech & The Math) |
|---|---|---|---|
| Compute & Orchestration | EC2 + EKS / Fargate | Hetzner Bare Metal / Cloud + RKE2 (Rancher) | Standard K8s API without the hypervisor overhead or the $70/mo control plane tax. |
| Data & Stateful Workloads | RDS / DynamoDB / SQS | Bare Metal/Dedicated vCPU NVMe Nodes + K8s Operators | Raw physical hardware IOPS for databases. Bypass slow network-attached storage and extortive Provisioned IOPS fees. |
| Storage (Object & Block) | S3 + EBS | Hetzner S3-Compatible + Longhorn (Block) | Standard S3 APIs backed by highly redundant Ceph, without the criminal data egress bandwidth fees. |
| Traffic & Edge Security | CloudFront + ALB + WAF | Cloudflare + Traefik Ingress | Flat-rate global caching, DDoS protection, and modern K8s-native routing out of the box. Stop paying per-GB processed. |
| Observability & Logging | CloudWatch / DataDog | Grafana LGTM (Alloy, Loki, Grafana) + Prometheus | Sub-second log querying and deep metrics without the $5,000/month ingestion and retention bill. |
| Deployment & GitOps | CodeDeploy / CloudFormation | ArgoCD / Flux | Your infrastructure and deployments are version-controlled in Git. The system is the documentation. Zero proprietary lock-in. |
What Does The Stack Include?
Hybrid Kubernetes with Rancher RKE2. Spikes burst to Cloud automatically.
Bare Metal NVMe Nodes with automated backups and PITR.
Cloudflare DDoS protection, Traefik routing, and encrypted secrets.
Grafana LGTM stack monitoring and declarative ArgoCD deployments.
Day 2 Operations: The Trust Builder
To keep this service affordable and sustainable, we adhere to a strict “Infrastructure vs. Code” boundary. We run the platform; you run the code.
We Handle (Platform Engineering)
- Server Uptime & K8s API: Ensuring the cluster is healthy.
- Database Availability: Keeping Postgres/Redis running and backed up.
- CI/CD Pipeline Health: Ensuring the runners are active.
- Security Patching: OS and Cluster level updates.
- Scenario: “The database drive is full.” -> We fix it.
You Handle (Product Engineering)
- Application Logic: Fixing bugs in your code.
- Database Queries: Optimizing slow SQL queries.
- Dependency Updates: Updating npm/pip packages.
- Scenario: “I pushed bad code and the site is 500ing.” -> You fix it (We help rollback).
Curious about your potential savings?
Most teams save 40–60% on cloud compute. Use our free calculator to see exactly how much you could save.
Ready to Take the Next Step?
If the calculator shows meaningful savings, here’s what to do next:
Technology Stack FAQ
What does “No Lock-In” really mean?
We build your infrastructure entirely using CNCF-certified open-source tools. Everything is provisioned with Terraform, configured with Helm, and deployed via GitOps. If you leave, you take your Terraform state and your data—no proprietary APIs or opaque “managed services” to rewrite.
How do you run databases faster than public cloud RDS?
We bypass slow, network-attached block storage (like EBS) and provision dedicated bare metal servers or vCPU nodes using locally attached NVMe storage. You get the raw IOPS of physical hardware, drastically reducing latency and avoiding AWS’s provisioned IOPS fees.
Do you use EKS or GKE?
No, we run RKE2 (Rancher Kubernetes Engine 2) directly on Hetzner infrastructure. RKE2 is a fully conformant Kubernetes distribution optimized for security. This eliminates the $70/month control plane tax of managed cloud K8s services while providing exactly the same API.
How is stateful storage handled in Kubernetes?
We use Longhorn for block storage in the cluster, which synchronously replicates volumes across multiple nodes. For high-performance databases, we use hostPath or local persistent volumes to map directly to local NVMe drives.
What tools do you use for CI/CD?
We strongly advocate for a GitOps approach. We use ArgoCD or Flux to automatically sync your cluster state with your Git repositories. Your system is self-documenting and instant rollbacks are as simple as a git revert.
How do you handle monitoring and logging?
We use the Grafana LGTM stack (Loki, Grafana, Tempo, Mimir) paired with Prometheus. This gives you deep metrics, distributed tracing, and sub-second log querying without the extortionate data ingestion and retention fees charged by Datadog or CloudWatch.
Is your network and edge secure?
Yes. We route external traffic through Cloudflare for global caching, WAF, and DDoS protection before it hits our Traefik ingress controllers. Ingress communication is encrypted via automated Let’s Encrypt certificates.
How do you handle infrastructure as code (IaC)?
All foundational infrastructure (servers, load balancers, firewalls) is defined in Terraform. Kubernetes-level configuration and application deployments are handled via Helm charts and ArgoCD. There are no manual “click-ops.”
Can you migrate existing AWS infrastructure to this stack?
Yes. We offer an Infrastructure Audit and Shadow Run / Managed Platform migration services. We assess your current architecture, identify stateful vs. stateless workloads, and seamlessly move your compute to our open stack while managing database replication to avoid downtime.
Do you manage OS and Kubernetes updates?
Yes, patching is core to our “Day 2 Operations.” We handle node OS patching, Kubernetes control plane upgrades, and automated etcd backups so your developers can focus purely on application code.
discovery Zoom. We'll review your current cloud spend, identify what's safe to move, and give you an honest Go / No-Go recommendation — no commitment, no sales pitch. If the numbers work, we'll show you how. If they don't, we'll tell you that too.
Interested? Contact us.
Check out our RSS Feed to keep up with the cloud repatriation news